Simulation model for Web-of-Cells cyber security analysis
Short description
A model of the Information and Communication Technology (ICT) architecture comprising different topological solutions underlying the Web-of-Cells (WoC) concept, extended with security features and measures, for the analysis of possible attack paths and their success likelihood.
Main technical features
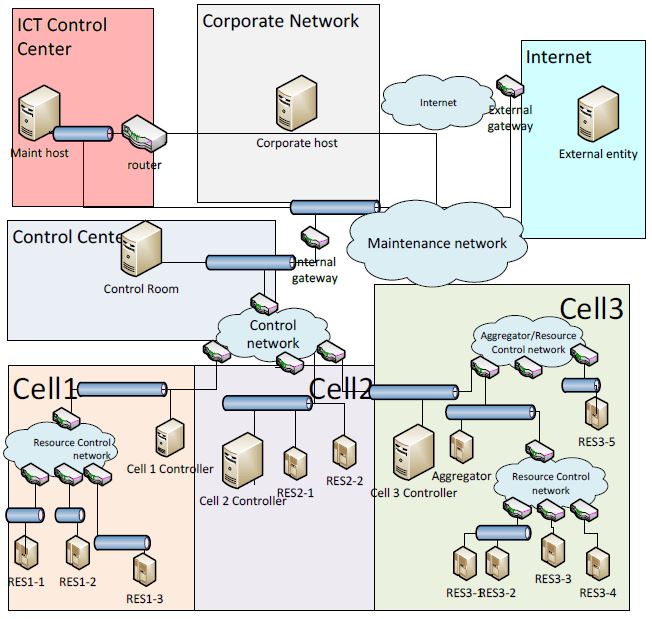
A securiCAD model of the Information and Communication Technology (ICT) architecture deployed for the execution of the Web-of-Cells (WoC) control strategies. The model addresses several WoC-specific ICT topologies with different hardware and software assets. Fig. 1 shows the general ICT architecture of the WoC represented in the securiCAD model.
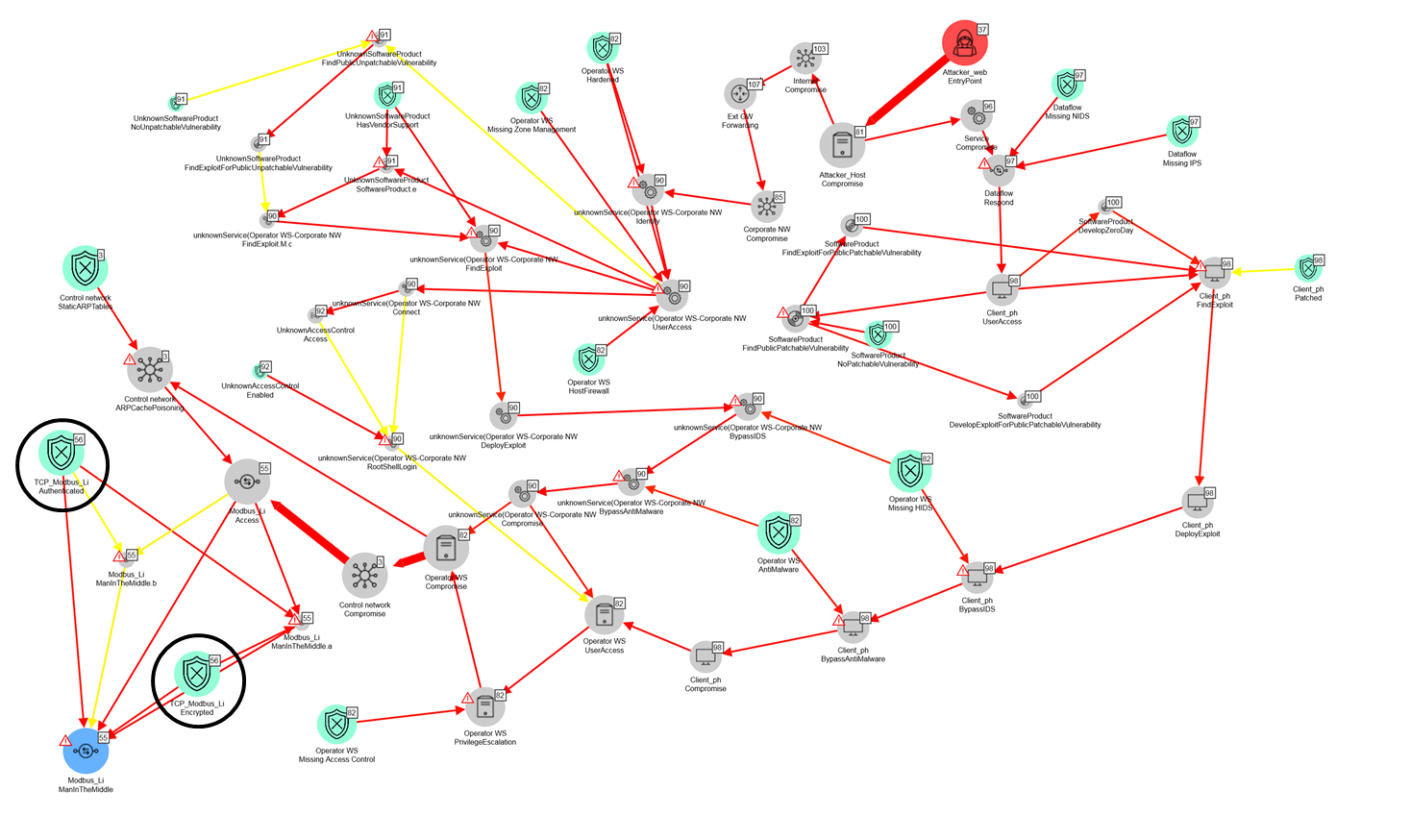
The model allows to estimate the threat likelihoods in relation to architecture variants in terms of asset features and cyber security measures. Once cyber security countermeasures are included into the model, with securiCAD it is possible to evaluate their effectiveness considering the attack paths automatically generated by the tool. Figure 2 presents an attack graph including the most frequently traversed and least resilient attack paths in the securiCAD simulations from the model of the previous WoC architecture. The source is the attacker (red circle) and the target (blue circle) is the attack step of compromising a cell resource. The attacker performs a “Man In The Middle” attack to the data flow between the cell 2 controller and the resource 2-2 in the Cell 2 architecture. The attack graph involves different assets and weaknesses that the attacker may exploit in order to progress with the attack process. The evaluation of the TTC values depends on the analysis of the whole attack graph.
From the analysis of the model it is possible to obtain the steps of the main attack paths and evaluate the Time To Compromise (TTC) for the more critical assets. The model simulations support the selection of suitable security countermeasures and the evaluation of their effectiveness through a sensitivity analysis of the TTC values.
A more detailed description of the model is reported in Attachment 1. The two models developed for the attack analysis to the WoC (extended and field test) architectures are available in Attachment 2.
Innovative aspects
Technology Readiness Level: TRL4
Applications
The model can be used freely for research/educational purposes